how to remove a hacker from my phone app
Once the app has been installed it can keep on tracking the text messages for you. You may have to contact the app provider and ask them to remove your information.

Top 3 Methods To Hack Or Unlock Any Android Pattern Lock Pin Password In 2017 Easily These Are The Working Smartphone Hacks Android Hacks Android Phone Hacks
Removing bad apps is a lot easier on your iPhone than it is on say a PC.

. How can mSpy help track the location of the iPhone. So if a hacker gets in to an enabled account they get to choose. Is the Authenticator app replacing the codes that lands as text message.
Monitoring and accompanying your children on the Internet is an idea that goes through the heads of all. Remove both Outlook profiles in the app data folder. Check for inaudible sounds on your phone by using a sound-bandwidth sensor on a low frequency.
So if you dont recognize an app it doesnt necessarily mean its. Of course some unnecessary apps come pre-installed on new phones these are called bloatware. 3D touch malfunctions badly with a slightly swelling battery pressing against the lcd backplate inside the phone.
The sandboxed Google services compatibility layer using device profiles lets you have your privacy cake and eat proprietary apps when you need them. I know that you will not always have access to your boyfriends phone but with the spy app you will get first-hand information. Ran the Microsoft Support and Recovery Assistance Tool.
This will make it difficult for the hacker to re-enter your device. I saw malfunctioning 3d touch several times every week back when I was in phone repair. KidsGuard Pro is invisible on the target phone so you dont have to worry about being caught.
Your kid would have to become a nation state level hacker to do bad things on there and if he does. If you have or are willing to buy a compatible phone GrapheneOS is as good as it gets in my experience -- pushes the envelope of usability and security more than any other mobile device OS yet. Their password manager app is used and loved by millions.
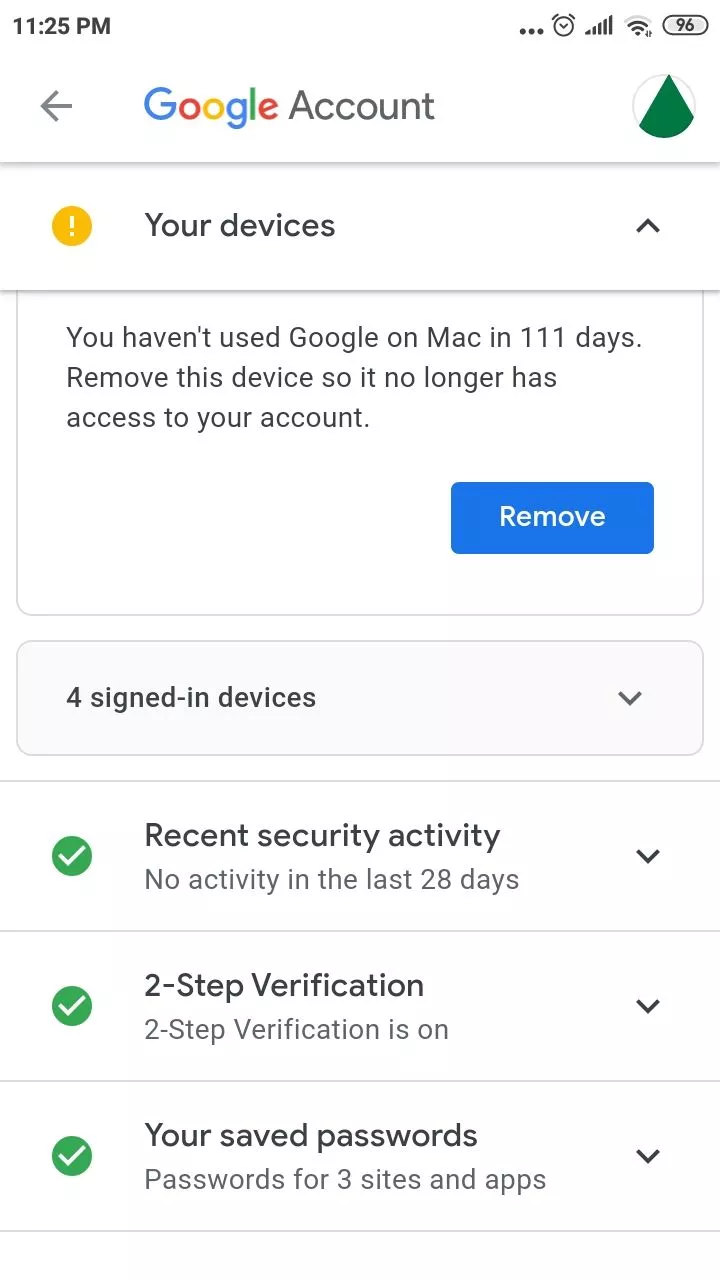
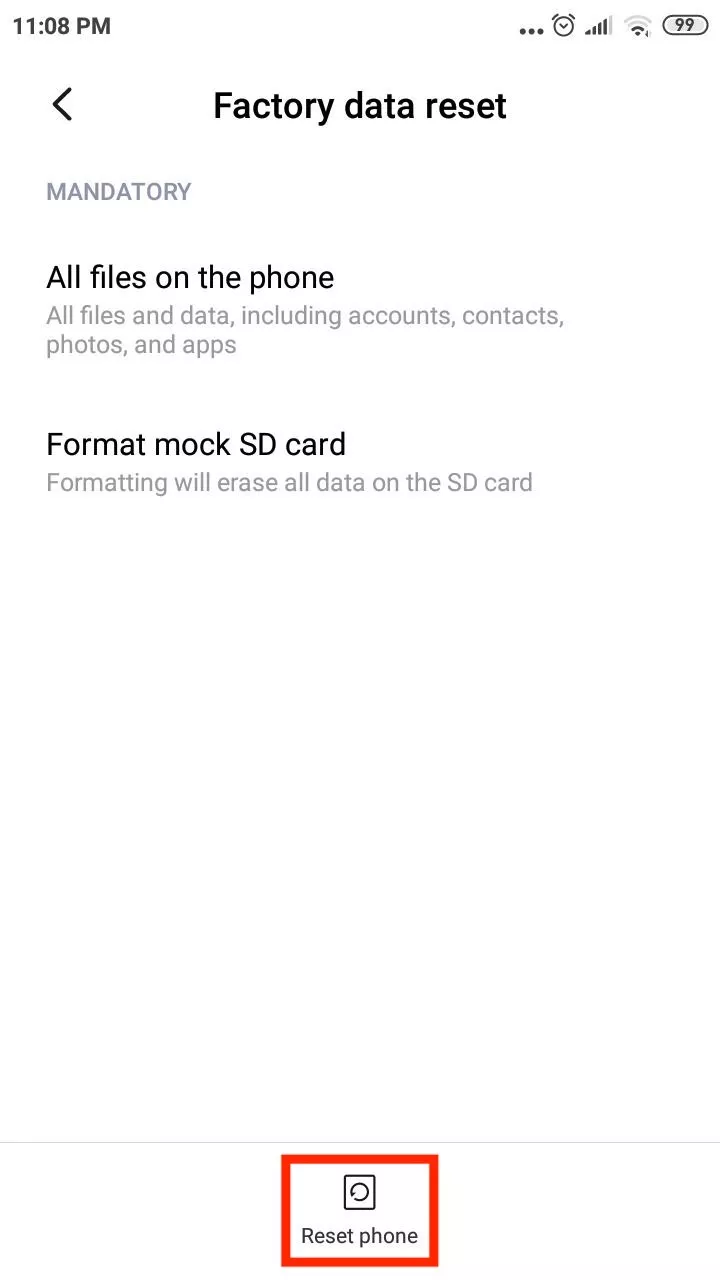
You then need to put all your info on every device on a cloud or take everthing to a. Normally each iPhone has a unique 15 digit code called IMEI number and this number can be accessed by entering 06 on your phones call screen. The only way to completely remove malware is by doing a factory reset.
Please click on the iCloud logo in the My Devices box in the upper left corner of the screen to return to the iCloud home screen. Using The Ultimate Phone Spy App. Please click on Sign Out in the upper right corner to exit.
Desktop version and the online version and emails mapped on my phone do I need both. For instance launching a specific app feature or workout. If youve inadvertently installed a bad app on your iPhone you can uninstall the app to get rid of it.
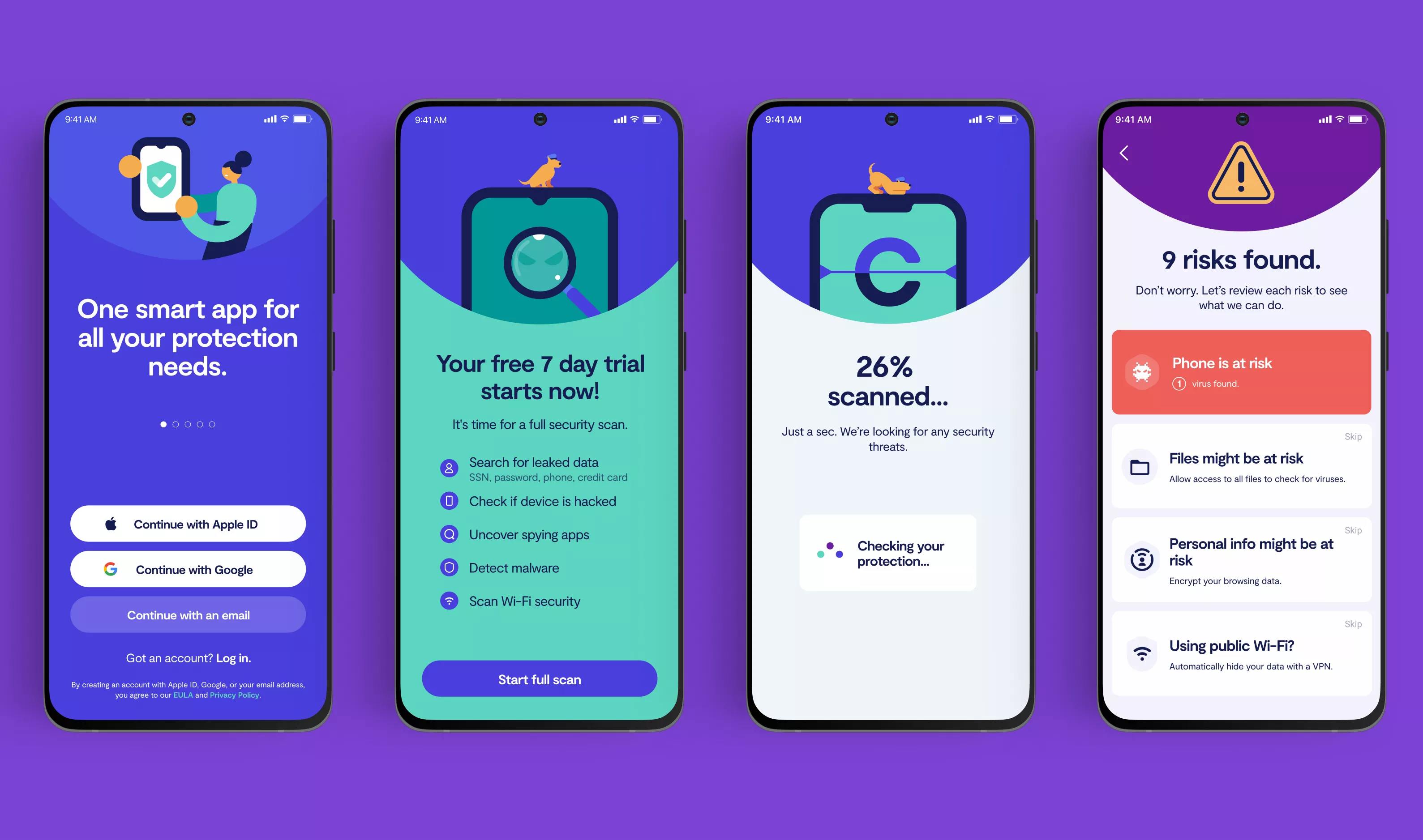
Perform scans frequently and keep your updates well up to date. The 6s case was bent for every person who carried it in their back pocket. This number code cannot be altered or removed from your iPhone making it easier to locate a lost iPhone without iCloud even if it is being used with another SIM or being powered off.
Going from 12MP up to 48MP for the first time. Theft and a single day of effort could result in your phone being breached. The app also lets you backup this data to your LastPass account in case you need to switch phones or lose the current one.
Avoid torrent sites illegal downloads and never ever open an app from an unknown source even if it comes to you under the guise of a known email contact. First youll need to reboot your phone into safe mode. The first one is the Ultimate Phone Spy App and that too for great.
To delete an app just tap and hold its icon and select Delete App or tap the X on the app if the icons start jiggling. Remove all unnecessary apps from your phone or tablet. If you have a wifi box disconnect everything.
There are many reasons for high data usage for example increased use of a new app. Easy and Effective Tools To Hack Any Android Phone By Sending A Link. A sound-bandwidth sensor is a noise detector app from another phone that could be used to measure sound on a potentially tapped device.
Com This guy totally amazed me as he produced an end to my long wanting task within 6 hours i was viewing everything my partner been doing on their phone. Malware is a type of virus that can infect your phone and give the hacker access to your device. The authenticator app lives up to that promise and does the job flawlessly.
Also its smart to go through your apps regularly and check out the privacy settings. If you can keep your phone with you a hacker will have to work much harder to get into it. If it finds sounds several times in one minute your phone may be tapped.
That means this will be the first phone can record 8K 30fps video thanks to the most powerful next generation Apple A16 Bionic. Always use a passcode lock and use complex passwords. Strange apps that you didnt install shouldnt end up on your phone.
Here we will provide you the easy-to-use and effective tools to hack an android phone by sending a link. And cached images and files. If a hacker gains access to your device they may be able to use that information.
In many cases an iPhone hack involves malware. Follow the instructions from the app to remove the spyware and any other threats that may be lurking. Physical access is the easiest way for a hacker to corrupt your phone.
Remove apps you dont recognize. Keep your phone with you at all times. Or a bend in the phone chassis.
To factory reset your phone follow the instructions from Apple. Second thing upgrade wifi box and put a fire wall on the box. Thats all it takes to become spyware-free.
Safe mode prevents all third. I have tried many services but always get ripped off without getting noting in return but a colleague at work introduced me to this loyal man of his word guy H A C K Q U E E N 3 gmail. Higher than normal data usage.
So if you notice texts or calls from your phone that you didnt make you may have had your phone hacked. Finally even before all the above precautions download a reputable cybersecurity program for your PC or mobile phone. But if your phone behavior has stayed the same and your data usage has skyrocketed its time to investigate.
If you notice an app on your phone that you didnt put there a phone hacker might be responsible. Your boyfriend is not aware that he. You can add all your Google Facebook Twitter Dropbox and more 2FA keys here.
Now its time for the most awaited section. If you want to root out the issues on your own here are the steps to take.

How To Unlock Android Pattern Lock Without Losing Data Youtube Iphone Life Hacks Life Hacks Computer Smartphone Hacks

What To Do If Your Phone Has Been Hacked
How To Remove A Hacker From My Phone
How To Remove A Hacker From My Phone

How To Remove A Hacker From My Phone An Easy Guide 2022

How To Stop Phone Hacking How To Know Your Smartphone Is Hacked Youtube

How To Remove A Hacker From My Phone

3 Simple Ways To Fix A Hacked Android Phone Wikihow
How To Remove A Hacker From My Phone
Signal Hacked Cellebrite S Phone Hacking Software Used By Law Enforcement Engadget

How To Remove A Hacker From My Phone An Easy Guide 2022

How To Remove A Hacker From My Phone In Depth Easy Guide
How To Remove Hackers From Your Phone How To Know Phone Hacked Or Not In Telugu Call Log Setting Youtube

Has Your Smartphone Been Hacked Battery Drain App Woes To Data Spike 5 Signs To Look Out For And How To Stop It Mobile News

How To Remove A Hacker From My Phone An Easy Guide 2022

How To Remove A Hacker From My Phone An Easy Guide 2022

How To Check If Your Iphone Has Been Hacked And How To Remove Hacks Youtube

